Is Your Business Held Together with IT Duct Tape? Here's How to Tell You Need a Managed Service Provider
Here's How to Tell You Need a Managed Service Provider
Is Your Business Held Together with IT Duct Tape?
So here's the deal. If you're running a small or medium-sized business, you're probably juggling way too many roles. One minute you're the CEO, the next you're in sales mode, then suddenly you're playing IT support guy because Karen in accounting can't remember her password. Again.
And look, I get it. You've figured out how to restart the router (unplug it, count to ten, plug it back in). You can reset passwords in your sleep. There's supposedly a backup system running somewhere—you set it up back in 2022, maybe 2021?—and you're like 80% sure it still works. Maybe 70%.
Sound about right?
Here's the uncomfortable truth: while you've been busy keeping your business afloat and taking care of customers, technology has quietly become the backbone of literally everything you do. And that whole duct-tape approach to IT? It's not just holding you back. It's putting your entire business at risk.
You might be thinking "I don't really need a Managed Service Provider." But if you're dealing with constant tech fires, losing sleep over cybersecurity, or watching your team burn hours on IT headaches instead of actual work, you're already paying the price. You're just paying it in a different currency—time, stress, and lost opportunities.
Let me walk you through the warning signs, what an MSP actually does (beyond the corporate jargon), and if you decide you need one, how to pick a partner that won't let you down.
The Warning Signs: When Your DIY IT Strategy Falls Apart
Before we get into the whole "what is an MSP" thing, let's figure out if you actually need one. According to the experts at Gartner, most businesses don't realize they need professional IT help until something goes catastrophically wrong (Gartner). Like, really wrong.
Here are the red flags screaming that you've outgrown your current setup:
Your team spends more time playing tech support than doing their jobs. When your top salesperson is on hold with Comcast instead of closing that big deal, or your accountant is troubleshooting printer issues instead of, you know, accounting—that's a problem. It's a productivity crisis wearing an IT costume.
You're not actually sure if your backups work. Be honest. When's the last time you tested a restore? Do you even know what's being backed up? Where it's going? Yeah. That's what I thought. This is basically Russian roulette with your business data.
Cybersecurity is that thing that keeps you up at 2 AM. You see the news about ransomware attacks. The data breaches. The companies that went under because of one phishing email. And you wonder—could we be next? Meanwhile, your employees are using "Password123" for everything, and you're not entirely sure if that antivirus subscription expired months ago or if it's still... doing something.
Everything breaks all the time. Computers running like molasses. Network crashes every Tuesday (or is it Wednesday?). Applications that freeze during the exact moment you need them most. You're basically a professional firefighter at this point, except the fires are digital and there's no end in sight.
There's no IT strategy—just chaos and reactions. You buy stuff when it breaks or when someone complains loud enough. There's no plan. No budget that makes sense. And if someone asked you where your technology should be in six months? Five years? You'd probably laugh nervously and change the subject.
If you're nodding along to any of this, stick with me. You're definitely not alone, and there's actually a better way forward.
What Exactly Is a Managed Service Provider? (Without the Corporate Nonsense)
According to Gartner's official definition, an MSP is "a company that remotely manages a customer's IT infrastructure and end-user systems" (Gartner). Which, okay, technically accurate but also super boring and doesn't really tell you what that means for your actual business.
Think of it this way: an MSP is basically your entire IT department—the strategist, the help desk people, the security experts, the advisor who tells you what tech you actually need—all wrapped up in one outside partner. Instead of trying to hire full-time IT staff (which most small businesses can't afford and don't really need), you partner with an MSP that handles all your tech stuff for one predictable monthly fee.
TechTarget puts it a bit differently, saying MSPs provide "proactive management, monitoring, and problem resolution" instead of the old break-fix model where you only call someone after everything's already on fire (TechTarget). And honestly? That proactive part is the game-changer that transforms how your business runs.
What Should Your MSP Actually Do? (The Real Stuff, Not the Brochure Talk)
A good MSP doesn't just show up when stuff breaks. Based on what industry guides recommend, here's what you should actually expect:
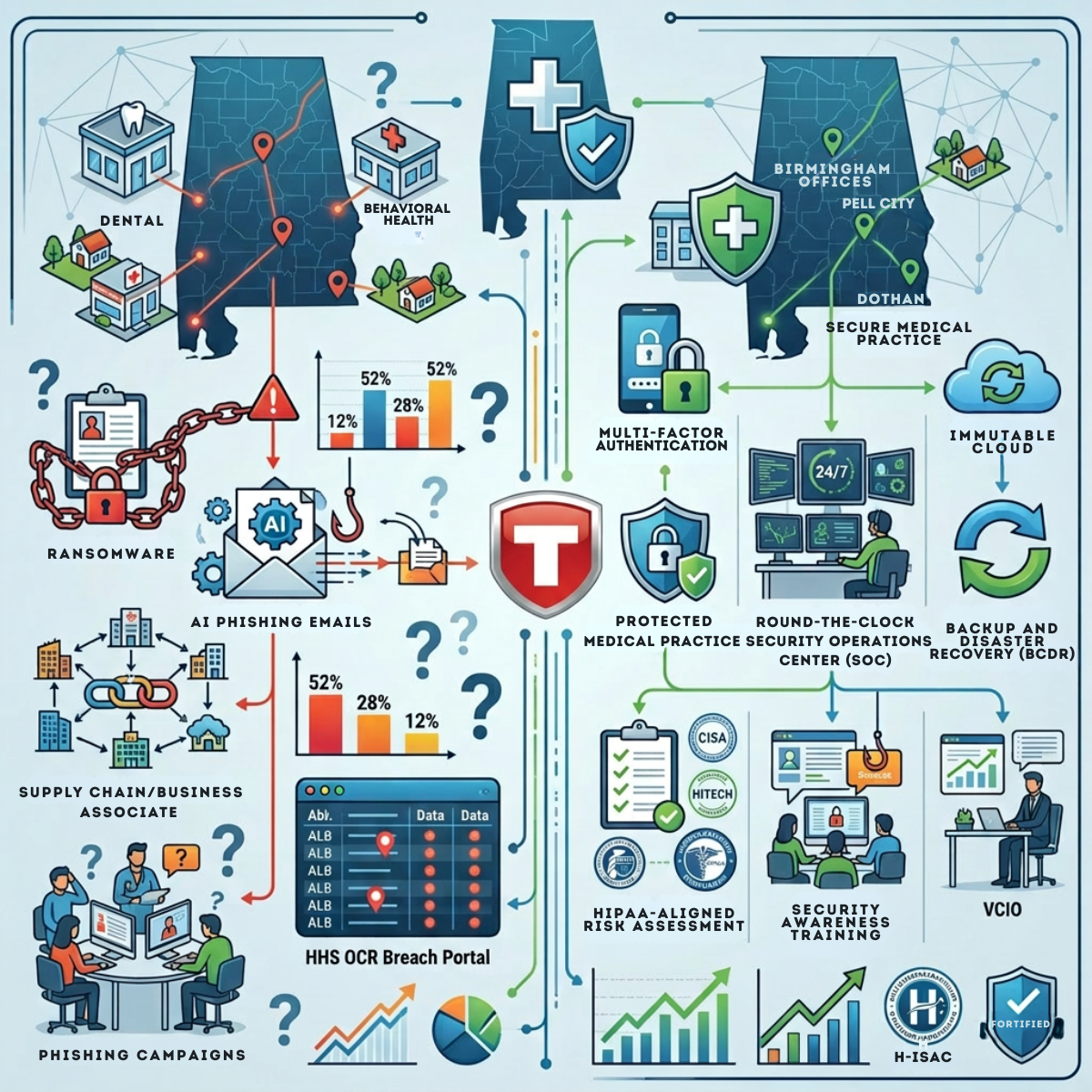
They Monitor Your Stuff 24/7: Your MSP should be watching your systems around the clock, catching problems before they blow up into full-scale disasters. Servers, network, security threats—all of it (NinjaOne). Think of it like having a security system for your house, except it's for your technology.
They Actually Plan for the Future: Beyond just keeping things running, your MSP should be helping you think strategically. What tech investments make sense? When should you upgrade? How does all this align with where you want to take your business? (Forbes Business Council).
They Take Security Seriously: In 2025, cybersecurity isn't some nice-to-have extra. Your MSP should provide real protection—firewalls, antivirus that actually works, email security, training your employees to spot sketchy stuff, and a plan for when (not if) something happens (Cynet).
One Number for Everything: When something goes wrong, your employees shouldn't have to figure out whether to call the email vendor, the software company, or the hardware guy. Your MSP should be the single point of contact for all of it (CMIT Solutions). One call, one ticket, done.
Backups That Actually Work: Regular backups, secure storage, fast recovery when disaster strikes. But here's the key—they should actually test these backups. Not just assume they're working and find out they're not when it's too late (Compass MSP).
Compliance Help: Depending on what you do—healthcare, finance, whatever—you might need to comply with regulations like HIPAA or PCI-DSS. Your MSP should get this stuff and help you stay compliant without losing your mind (LANSA).
What Actually Changes When You Get the Right MSP?
Forbes Business Council talks about how the right MSP partnership should tackle your specific pain points and tie your tech strategy to your actual business goals (Forbes Business Council). When that happens—and it's not just empty marketing speak—small businesses usually see some pretty major shifts:
You Can Actually Budget for IT: No more surprise $5,000 bills when your server dies. You pay a consistent monthly amount. You can plan. You can breathe. No more financial ambushes.
Stuff Just... Works: Proactive monitoring means problems get fixed before they take down your whole office. And when things do go wrong, they get fixed faster because your MSP already knows your setup inside and out.
Real Security: Professional-grade security tools and expertise that would normally be way out of your budget. You get enterprise-level protection at small business prices.
Your Team Can Do Their Jobs: When technology works the way it's supposed to, people can focus on what they were actually hired to do. The time saved adds up fast across your whole company.
Access to People Who Actually Know This Stuff: Instead of depending on one overwhelmed IT person (or your nephew who's "good with computers"), you get a whole team of specialists. Networking, security, cloud services—the works.
Room to Grow: As your business expands, your IT can grow with it. Your MSP plans for it and supports it without the usual chaos and panic.
How to Actually Choose the Right MSP (A Framework That Works)
Okay, so you've decided you need an MSP. Now comes the hard part—picking the right one. There are literally thousands out there. How do you separate the good ones from the ones who'll just take your money and disappear when you need them?
1. Figure Out What You Actually Need First
Before you talk to anyone, sit down and document where you're at and where you want to go. Kelser Corporation recommends getting really clear on your current infrastructure, your pain points, what you can actually afford, and your growth plans (Kelser Corporation). This prep work means you'll ask better questions and actually be able to tell if a potential MSP gets what you're dealing with.
2. Look at Their Experience and Expertise
Not all MSPs are the same—like, at all. LANSA emphasizes finding someone with actual experience in your industry and with businesses your size (LANSA). An MSP that mostly works with Fortune 500 companies probably won't understand what it's like to run a 50-person operation. And if you're in healthcare, you need someone who knows HIPAA inside and out, not someone who'll learn on your dime.
Ask them:
- How long have you been doing this?
- How many clients do you have in my industry?
- What's the typical size of your clients?
- What certifications do you have?
- Have you worked with our specific tech before?
3. Get Clear on Service Level Agreements (SLAs)
Service Level Agreements are basically promises in writing—response times, fix times, uptime guarantees, and what happens when they don't deliver. NinjaOne calls SLAs one of the ten critical factors because they turn vague promises into actual commitments (NinjaOne).
Dataprise recommends asking specific questions: "How fast will you respond to critical issues? What about the non-urgent stuff? Do you have different support levels? What happens if you miss these commitments?" (Dataprise).
If an MSP is vague about SLAs or doesn't want to put things in writing? Run. The good ones back up their service with real, measurable guarantees.
4. Don't Skimp on Security
Cynet's 2025 buyer's guide is pretty clear: cybersecurity needs to be core to any MSP relationship, not some optional add-on you pay extra for (Cynet). Your MSP needs to provide multiple layers of security and actually know what they're doing when it comes to threats.
Key questions:
- What security tools do you use?
- How do you monitor for threats?
- Do you train our employees on security?
- What's your incident response process?
- How do you stay current with new threats?
- Do you have cyber insurance? Am I covered?
5. Understand How Support Actually Works
When something breaks, how fast do you get help? Who do you talk to? Will it be the same person who knows your setup, or a different technician every time? CMIT Solutions says the support model matters because it affects your day-to-day experience with the MSP (CMIT Solutions).
Look for:
- Multiple ways to reach them (phone, email, portal, chat)
- Clear escalation for urgent problems
- A dedicated person managing your account
- Regular check-ins to review performance
- Transparent communication about what's happening
6. Understand the Pricing (Really Understand It)
MSP pricing usually works one of a few ways: per person, per device, tiered levels, or custom packages. Compass MSP warns against just picking the cheapest option—cheap usually means cheap service, but the most expensive doesn't automatically mean the best either (Compass MSP).
Instead, understand:
- What's actually included in the base price?
- What costs extra?
- Are there setup fees?
- How long is the contract? What if we need to cancel?
- What happens to the price when we add people or services?
The right MSP gives you transparent pricing that makes sense for what you're getting.
7. Actually Check References (Don't Skip This)
I know it seems obvious, but tons of businesses skip this step. LANSA recommends asking for references from similar businesses and actually calling them (LANSA).
Ask:
- How long have you worked with them?
- How were they during a crisis?
- Are they proactive or reactive?
- Would you choose them again?
- What could they do better?
Check online reviews too, but remember that small MSPs might not have tons of reviews, and angry people are way more likely to review than happy ones.
8. See If You Actually Click
Forbes Business Council points out that the best MSP relationships are real partnerships, not just vendor transactions (Forbes Business Council). You're going to work closely with these people. They're getting access to your most important systems. You'll be relying on them when things go sideways. The relationship needs to work on a human level, not just a technical one.
Pay attention to:
- Do they actually listen to you and ask good questions?
- Can they explain tech stuff without making you feel stupid?
- Do they seem to care about your success?
- Are they pushing services you don't need?
- Do they share your values?
Trust your gut. If something feels off during the sales pitch, it won't magically get better after you sign.
9. Ask About Their Tools
The tools your MSP uses directly impact the service quality. Dataprise recommends asking about their monitoring platform, ticketing system, security tools, and backup solutions (Dataprise). You don't need to become an expert, but knowing they use professional-grade, current tools matters.
10. Plan for the Transition
Switching to an MSP—or changing MSPs—involves a transition. Kelser Corporation says to ask about onboarding: How long? What do we need to do? How do you document everything? What if problems come up during the switch? (Kelser Corporation).
A solid onboarding process shows they've done this before and know how to make it smooth.
Red Flags to Watch Out For
Just as important as knowing what to look for is spotting the warning signs:
They're vague about everything: If they can't give you straight answers about processes, pricing, or what they actually do, that's a huge problem.
High-pressure sales tactics: "This deal expires tonight!" or "You need to decide now!" are red flags. Good MSPs don't need to pressure you.
Cookie-cutter solutions: Every business is different. If they're not taking time to understand your specific needs, how can they possibly serve them?
Either overproposing or underproposing: They should recommend what you actually need. Not the bare minimum. Not every possible service under the sun. What you need.
Hard to reach during sales: If they're slow to respond or hard to get hold of now, imagine what it'll be like when you're a paying customer.
What's Next?
If you recognized yourself in those warning signs at the beginning, you're in good company. Most small and medium businesses hit a point where the DIY approach stops working. The question isn't really whether you need professional IT help—it's whether you'll make that change now, on your terms, or wait until something catastrophic forces your hand.
The good news? Choosing the right MSP doesn't have to be overwhelming. Use this framework. Ask the right questions. Take your time finding someone who actually fits. You can turn IT from a constant source of stress and surprise expenses into something that actually helps your business grow.
Your technology should work for you, not against you. With the right MSP partner, it finally will.
Stop Holding Your Business Together with IT Duct Tape
Get a real IT plan, 24/7 monitoring, tested backups, and security that actually works.
Book a 15-minute consult
Link: https://www.alltechsupport.com/contact-alltech-it-support#BookAMeeting
Or call 205-290-0215
Works Cited
CMIT Solutions. "15 Tips for Choosing an MSP." CMIT Solutions, www.cmitsolutions.com/resource-center/15-tips-for-choosing-an-msp. Accessed 13 Oct. 2025.
Compass MSP. "How to Choose a Managed Service Provider: The Ultimate Guide." Compass MSP, www.compassmsp.com/blog/how-to-choose-a-managed-service-provider. Accessed 13 Oct. 2025.
Cynet. "Managed Service Providers (MSP): 2025 Buyer's Guide." Cynet, www.cynet.com/managed-service-providers/. Accessed 13 Oct. 2025.
Dataprise. "12 Questions to Ask Managed Service Providers Before Hiring." Dataprise, www.dataprise.com/resources/12-questions-to-ask-managed-service-providers/.. Accessed 13 Oct. 2025.
Forbes Business Council. "What Businesses Should Consider When Partnering With An MSP." Forbes, www.forbes.com/councils/forbesbusinesscouncil/. Accessed 13 Oct. 2025.
Gartner. "MSP (Management Service Provider) - Definition." Gartner IT Glossary, www.gartner.com/en/information-technology/glossary/msp-management-service-provider. Accessed 13 Oct. 2025.
Kelser Corporation. "How To Pick The Right MSP: 8 Criteria To Evaluate." Kelser, www.kelser.com/blog/how-to-pick-the-right-msp. Accessed 13 Oct. 2025.
LANSA. "13 Tips for Choosing a Managed Service Provider (MSP)." LANSA, www.lansa.com/blog/13-tips-choosing-managed-service-provider.htm. Accessed 13 Oct. 2025.
NinjaOne. "10 Factors to Consider When Choosing An MSP." NinjaOne, www.ninjaone.com/blog/factors-to-consider-when-choosing-an-msp/. Accessed 13 Oct. 2025.
TechTarget. "What is a managed service provider (MSP)?" TechTarget, www.techtarget.com/searchitchannel/definition/managed-service-provider-MSP. Accessed 13 Oct. 2025.