Let's Talk Real Numbers (Because Nobody Else Will)
Here's something that'll probably annoy you: try finding actual IT service pricing online. Go ahead, I'll wait.
Frustrating, right? Most Managed Service Providers treat their pricing like it's some kind of state secret. You've got to sit through sales calls, fill out forms, maybe sacrifice a goat... okay, maybe not that last part, but you get the idea. It's ridiculous, honestly.
The short version? Most small to medium businesses end up paying somewhere between $100 and $250 per person each month for comprehensive IT support. But (and this is a big but), the way that pricing is structured makes a massive difference in what you actually get.
Look, I get why they do it. Every business is different, and IT needs vary wildly. But come on. You need to budget. You need ballpark figures before you waste time on sales calls. That's just basic business sense.
So here's what we're gonna do. I'm laying out exactly how MSPs charge, what you should expect to pay, and which pricing models actually make sense for different types of businesses. No secrets, no "contact us for pricing" nonsense.
Why You Should Actually Care About Pricing Models
Now, this might sound strange, but the pricing model matters way more than the actual price. Seriously.
Think about it this way: some pricing structures basically encourage your IT company to sit around waiting for things to break. Others... well, they incentivize actually preventing problems before they happen. Which one do you want?
Understanding how MSPs charge helps you:
- Actually budget for IT (revolutionary concept, I know)
- Avoid those "surprise" bills that aren't really surprises to anyone but you
- Make sure your IT provider's incentives line up with yours
- Compare apples to apples when you're shopping around
- Negotiate without getting taken for a ride
Alright, let's dig into the actual models.
The 8 Ways MSPs Will Try to Charge You
1 Hourly Rate (The "Break-Fix" Model)
How it works: You pay by the hour, usually only when something's broken or you need specific work done. This is old-school IT support, the way things worked before "managed services" became a thing.
What's included: Whatever you ask for. Troubleshooting, fixes, installations, advice. But here's the catch... nothing happens unless you pick up the phone and call.
The good stuff:
- Cheapest option if you genuinely have minimal IT needs
- Super simple to understand
- No contracts tying you down
- You only pay when you actually use it
The not-so-good stuff:
- Your monthly bills are basically a mystery
- Everything's reactive... you're always playing catch-up
- Your IT company literally makes MORE money when things break (think about that for a second)
- Can get insanely expensive during emergencies
- They never really learn your business
Who this works for:
- Really small startups with like 1-3 people
- Businesses that barely use technology
- Companies with solid internal IT who just need occasional specialized help
My take: Here's the thing... hourly pricing LOOKS cheap upfront, but it usually ends up being the most expensive option long-term. You're paying premium rates when everything's on fire, and your provider has zero incentive to install smoke detectors, if you catch my drift. Plus, as one industry report pointed out, this creates "inconsistent/unreliable income for MSPs," which... yeah, that inconsistency tends to trickle down to you.
2 Block Time (Prepaid Hours)
How it works: You buy a chunk of hours upfront each month, usually 10, 20, or 30 hours at a discounted rate. Use 'em or lose 'em, because they don't roll over. Go over your allotment and you pay extra.
What's included: General IT support and services. Most providers will ping you when you've got about 2 hours left so you don't blow past your limit.
Key details:
- Hours reset every month (no banking them)
- Usually auto-pays from your bank account
- Cheaper per hour than straight hourly billing
- Creates a predictable baseline expense (kind of)
The good stuff:
- Way more predictable than pure hourly billing
- Gets you in the habit of regular IT check-ins instead of crisis-only calls
- Saves you $10-25 per hour typically
- Industry folks call it a "growing MSP's best friend" as a stepping stone to full managed services
- Less commitment than going all-in on managed services
The not-so-good stuff:
- Still mostly reactive rather than proactive
- That end-of-month "use it or lose it" pressure is real
- You've gotta track and monitor usage
- Overage charges can still surprise you
Who this works for:
- Businesses moving from break-fix to managed services
- Companies not quite ready for the full commitment
- Organizations with 5-20 employees who need regular but not constant IT attention
My take: Block hours are honestly a pretty solid middle ground. According to one analysis I read, this model works as an effective "bridge to MSAs" (that's Managed Service Agreements for those not drowning in acronyms) while giving you more stability than pure hourly billing. It's like... IT training wheels, but in a good way.
3 All-You-Can-Eat Flat Fee (Unlimited Support)
How it works: You pay one fixed monthly rate per person that covers unlimited support, no matter how many hours your MSP actually puts in.
What's included: This is typically the full meal deal:
- Round-the-clock monitoring and alerts
- Regular maintenance and updates
- Remote help whenever you need it
- On-site support (though there might be limits)
- Strategic planning and consulting
- Help desk services
- Security management
Here's where it gets interesting from the MSP's perspective:
Dream client: Uses 1 hour/month = they're making $1,000/hour effectively
Nightmare client: Uses 25 hours/month = they're making $40/hour effectively
The good stuff:
- Your monthly bill is completely predictable
- Makes budgeting actually manageable
- Your team can use support freely without watching the clock
- Encourages proactive service (because the MSP benefits from preventing fires, not fighting them)
- Aligns everyone's incentives toward keeping things running smoothly
The not-so-good stuff:
- Can be pricey if you rarely have IT issues
- Requires careful upfront assessment to avoid getting mis-categorized
- MSPs need to set clear boundaries on what "unlimited" actually means
- Not all providers offer true unlimited... read the fine print carefully
Who this works for:
- Established businesses with 10+ employees
- Companies where technology is mission-critical
- Organizations tired of playing whack-a-mole with IT problems
My take: When it's done right, flat-fee unlimited delivers the best bang for your buck for most SMBs. But here's the catch. One industry study warned this model "can be disastrous when customers are misqualified" while also noting it "can bring big rewards when properly managed." Translation? If your IT provider won't thoroughly dig into your environment before quoting you, that's a massive red flag. Run.
4 Per-Device Pricing
How it works: You pay a flat monthly fee for each piece of equipment the MSP manages. Desktops, servers, printers, network gear... everything gets its own price tag.
What you'll pay:
- Desktop or laptop: $69/month
- Server: $299/month
- Printer: $29/month
- Network equipment: $49-99/month
These numbers vary, but that's the general ballpark.
The good stuff:
- Super easy to quote and understand
- Clear revenue projections for everyone
- Scales logically as you add infrastructure
- Transparent... you know exactly what you're paying for
The not-so-good stuff:
- Costs can spike fast if you add lots of equipment
- Doesn't work great with BYOD (Bring Your Own Device) setups
- Ignores how much actual user support is needed
- Might make you keep old equipment longer than you should
Who this works for:
- Businesses with standardized equipment
- Companies with clear device counts and minimal BYOD
- Organizations that can predict device additions pretty accurately
My take: Per-device pricing is straightforward and works well if you've got predictable, managed infrastructure. But as one expert pointed out, it gets messy in "BYOD environments" where people are bringing their own laptops and phones. And let's be honest, that's increasingly common these days.
5 Per-User Pricing
How it works: You pay one set fee per person that covers ALL their devices... laptop, phone, tablet, whatever they're using.
The good stuff:
- Incredibly simple for billing and budgeting
- Scales with headcount, not hardware
- Multiple devices per person? No extra cost
- Works beautifully with BYOD policies
- Easy to add or remove people as you grow or shrink
The not-so-good stuff:
- Might not match actual resource consumption
- Can be expensive for people with basic tech needs
- Doesn't really account for shared infrastructure costs
- Might overcharge light users or undercharge power users
Who this works for:
- Service businesses where everyone has similar tech needs
- Companies with BYOD policies
- Organizations where device counts per person fluctuate
My take: Per-user pricing has gotten really popular as people use more and more devices. It simplifies billing while accommodating how we actually work now. That said, it's not always the most cost-effective if your team's tech usage varies wildly.
6 Tiered/Bundled Packages
How it works: The MSP offers several preset packages (usually Bronze, Silver, Gold... or Basic, Professional, Enterprise... you get the idea) with different features and price points.
Typical structure:
- Bronze: Patch management + remote support $99/person/month
- Silver: Everything in Bronze + monthly on-site visits + backup management $149/person/month
- Gold: Everything in Silver + 24/7 emergency support + strategic consulting $199/person/month
The good stuff:
- Flexibility to pick your service level
- Clear differences between what each tier offers
- Natural upgrade path as you grow
- Can mix and match tiers for different groups
The not-so-good stuff:
- Too many options can make your head spin
- More complex to manage and bill
- Might pay for stuff you don't need just to get the features you want
- Tier definitions are all over the map between providers
Who this works for:
- Mid-sized businesses (25-100 employees) with different user needs
- Companies wanting room to grow
- Organizations preferring to pick and choose services
My take: Tiered pricing can work really well when the tiers actually make sense and reflect real business needs instead of arbitrary feature bundling. According to research I've seen, this model "adds flexibility" while allowing natural "upselling" as your needs mature. Just... make sure the tiers are logical and not just a way to force you into higher pricing.
7 À La Carte Pricing
How it works: Every service is priced separately. You build your own package from a menu of options.
Example menu:
- Help desk support: $50/person/month
- Monitoring: $25/device/month
- Backup: $35/person/month
- Security management: $75/person/month
- On-site support: $150/hour or $500/visit
The good stuff:
- Maximum flexibility and customization
- Only pay for exactly what you need
- Easy to add or drop specific services
- Shows you what each piece actually costs
The not-so-good stuff:
- Billing gets complicated with lots of line items
- Total monthly cost becomes unpredictable
- Time-consuming to manage and track everything
- Easy to miss important services when building your own package
Who this works for:
- Businesses with strong internal IT who can strategically pick services
- Organizations with unique or specialized needs
- Companies supplementing existing IT staff
My take: À la carte gives you maximum control, but it also creates billing headaches and makes comparing providers really difficult. It works best if you're pretty sophisticated and know exactly what you need. If you're reading this guide, you might not be there yet... and that's totally fine.
8 Value-Based Pricing
How it works: Pricing based on the value delivered to YOUR business, not on time, devices, or users. The MSP charges based on business outcomes, risk reduction, or strategic value.
Industry adoption:
59% of MSPs now use value-based pricing models. It's actually the most common approach according to recent research.
Example scenarios:
- E-commerce company: Pricing tied to uptime and transaction processing
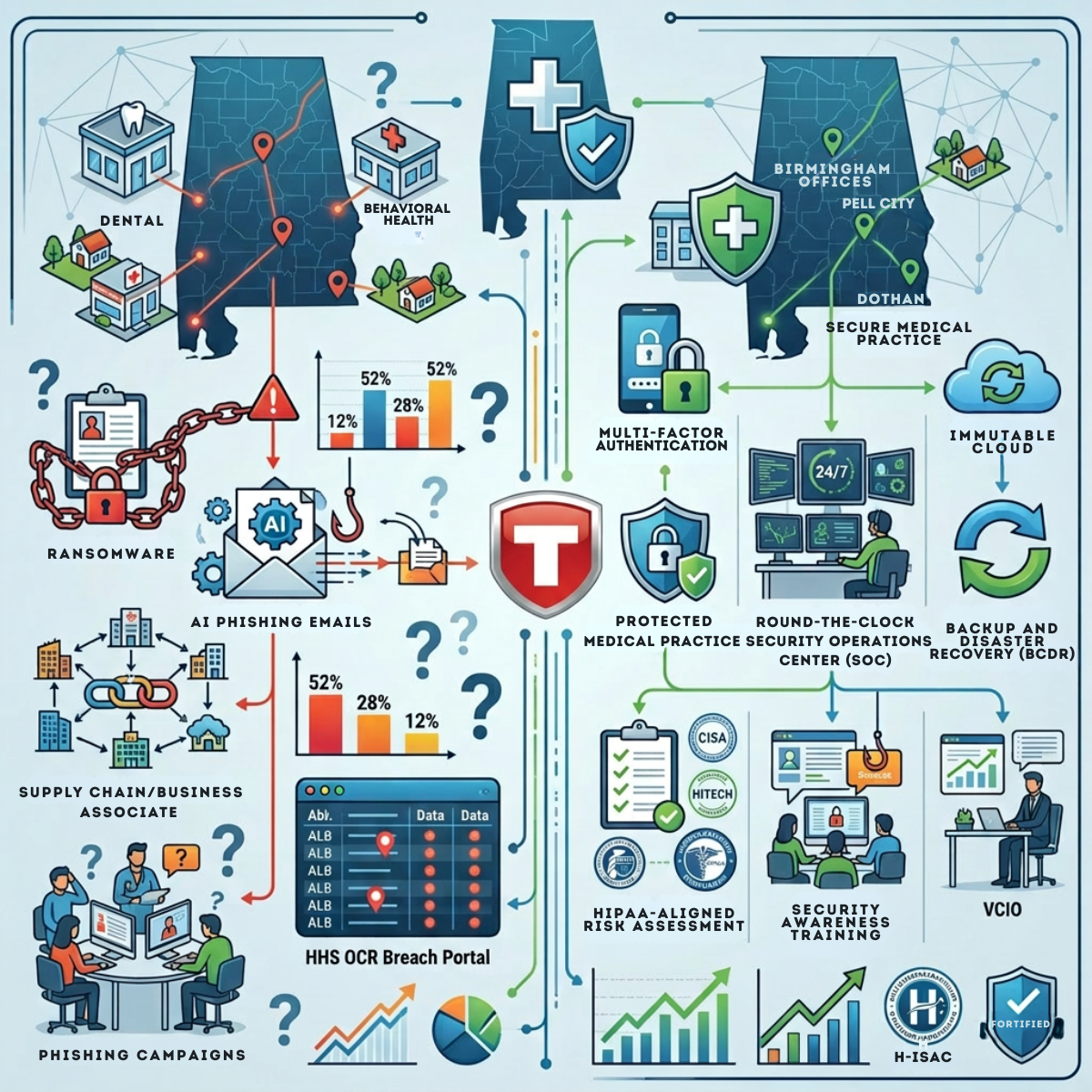
- Healthcare practice: Premium pricing reflecting HIPAA compliance and patient data protection
- Financial services: Higher rates justified by security requirements and regulatory stuff
The good stuff:
- Aligns what the MSP gets paid with actual business results
- Reflects real business impact instead of arbitrary metrics
- Can justify premium pricing for critical services
- Encourages strategic partnership instead of transactional relationship
The not-so-good stuff:
- Tough to quantify and communicate clearly
- Requires deep understanding of your business
- Harder to compare providers
- Can feel subjective
Who this works for:
- Businesses where IT is absolutely mission-critical
- Regulated industries
- Organizations seeking strategic IT partnership rather than just commodity service
My take: Value-based pricing is where the industry's headed, and honestly, it makes sense. But it only works with transparency and clear definitions of what "value" actually means. Otherwise it's just... vague.
Some Numbers That'll Help You Navigate This
Understanding what others are paying helps you evaluate whether you're getting a fair deal:
These stats from a 2025 industry analysis show that most MSPs have moved away from purely cost-based models toward value-based pricing. Make of that what you will.
Where the Industry's Actually Headed
This might help you pick a provider who's not stuck in the past:
| Level | Model | Description |
|---|---|---|
| Level 1 | Break/Fix (Hourly) | Old school reactive, pay when stuff breaks |
| Level 2 | Responsive (Block Hours) | Bridge phase with some predictability |
| Level 3 | Proactive | Actually trying to prevent problems |
| Level 4 | Managed (Fixed-Fee) | Full partnership model |
| Level 5 | Utility (Usage-Based) | Advanced consumption-based models |
Most experts recommend targeting Level 3 or 4 for optimal value. Levels 1 and 2 are basically... living in the past.
So Which One Should YOU Pick?
Got 1-5 employees with minimal IT needs?
Start with hourly or small block-hour packages. You probably don't need full managed services yet, and that's okay.
Got 5-20 employees and growing?
Block-hour contracts are probably your sweet spot. You get discounted rates and regular IT attention without the full commitment.
Got 20-50 employees?
Flat-fee unlimited or per-user pricing typically delivers the best value. Your IT needs are substantial enough to justify proactive management.
Got 50+ employees?
Tiered packages or value-based pricing lets you customize for different departments while keeping costs predictable.
In a regulated industry?
Value-based or premium tiered pricing that actually reflects your compliance and security needs.
🚩 Red Flags That Should Make You Run
No matter what pricing model they use, watch for these warning signs:
- Won't discuss pricing until you've sat through multiple sales presentations (your time has value too)
- Vague "unlimited" promises without documenting what that actually means
- Pricing way below market rates (you get what you pay for, folks)
- No clear service level agreements
- Pricing that doesn't include critical stuff like monitoring or security
Industry guidance consistently warns against "selling yourself short with rock-bottom pricing" because it usually means inadequate service. On second thought, maybe that's obvious.
❓ Questions You Should Definitely Ask
Before you sign anything:
- What exactly is included in this price?
- What costs extra?
- What are your actual response time commitments?
- How do after-hours emergencies work?
- What happens when we exceed hours/users/devices?
- What's your process for scope changes?
- Can you give me references from similar businesses?
- What's your average client retention rate? (This is a big one)
The Bottom Line
Look, there's no universal "best" MSP pricing model. It depends on your size, IT maturity, budget needs, and growth plans. But for most small and medium businesses, the sweet spot is usually one of these:
- Block hours if you're under 20 employees and transitioning from break-fix
- Flat-fee unlimited if you're established with 20-100 employees
- Per-user pricing if you've got BYOD policies and everyone uses multiple devices
And remember, cheaper isn't always better. Actually, it's rarely better. The research consistently shows that value-based pricing has become dominant because businesses are finally recognizing that IT service quality directly impacts business outcomes. Makes sense, right?
The goal is finding an MSP whose pricing model aligns their incentives with your success. When they win by keeping your systems running smoothly, everybody wins.
Works Cited
"MSP Billing Models: Which Is Best for Your MSP Business?" Syncro MSP, syncromsp.com/blog/msp-billing-models/. Accessed 10 Nov. 2025.
"MSP Pricing Models: Best Practice Strategies." SmarterMSP, smartermsp.com/msp-pricing-models/. Accessed 10 Nov. 2025.
"MSP Pricing Strategies." N-able, www.n-able.com/blog/msp-pricing-strategies. Accessed 10 Nov. 2025.
"MSPs Face Intensifying Pricing Pressure." Channel Insider, www.channelinsider.com/security/managed-services/msps-face-intensifying-pricing-pressure/. Accessed 10 Nov. 2025.
"Popular MSP Pricing Models and What's Best for Your Business." SuperOps, superops.com/blog/managed-service-provider/popular-msp-pricing-models-and-what's-best-for-your-business. Accessed 10 Nov. 2025.
"Pre-Paid IT Support Hours Agreement Template." NinjaOne, www.ninjaone.com/blog/pre-paid-it-support-hours-agreement-template/. Accessed 10 Nov. 2025.
"The Complete Guide to MSP Pricing Models." GetThread, www.getthread.com/blog/msp-pricing-models. Accessed 10 Nov. 2025.