DHS Biometric Search Engine: What SMBs Must Do Now
DHS Is Building a Unified Biometric Search Engine. Here's Exactly What Your Business Needs to Know.
The Department of Homeland Security is consolidating facial recognition, fingerprints, iris scans, and palm prints into one searchable platform across every major federal enforcement agency. The ripple effects reach your business — even if you've never thought of yourself as a biometrics company.
Executive Summary (TL;DR)
What's happening: On February 13, 2026, the U.S. Department of Homeland Security (DHS) issued a formal Request for Information (RFI No. 70RDA126RFI000003) to build a single, unified biometric "matching engine" — one interface for searching facial recognition data, fingerprints, iris scans, and palm prints across all major DHS components, including CBP, ICE, TSA, USCIS, and the Secret Service.
Why it matters to businesses: This initiative signals that biometric data is now among the most targeted categories of personally identifiable information (PII) in existence. Higher government investment in biometric infrastructure directly raises the black-market value of biometric records held by private businesses.
Who is already affected: Any business using fingerprint authentication, facial recognition time clocks, biometric access controls, Windows Hello, or Apple Face ID on company devices may already be storing regulated biometric data — often without knowing it.
What the law says: Illinois (BIPA), Texas (CUBI), and Washington (BPPA) already impose strict biometric privacy requirements on private businesses. Violations under Illinois BIPA can cost $1,000–$5,000 per individual scan.
The action item: Start with a Cybersecurity Risk Assessment. You cannot protect data you don't know you have. AllTech IT Solutions offers a no-obligation assessment that maps exactly where your business stands.
The Short Answer (Read This First)
On February 13, 2026, DHS published RFI No. 70RDA126RFI000003, formally asking private biometric technology contractors to help build one unified platform capable of matching any biometric identifier — face, fingerprint, iris, palm — across Customs and Border Protection (CBP), Immigration and Customs Enforcement (ICE), the Transportation Security Administration (TSA), U.S. Citizenship and Immigration Services (USCIS), the Secret Service, and DHS headquarters. (Source: Biometric Update, February 18, 2026; WIRED)
This is not a proposal under review. It is an active procurement initiative with a response deadline of March 4, 2026, backed by a $271.7 million congressional recommendation for DHS's Office of Biometric Identity Management (OBIM).
For Alabama small and medium businesses, the implication is direct: when the federal government treats biometric data as national infrastructure worth billions of dollars, that data becomes one of the most targeted assets in the cybercrime economy — including the biometric data your business may already hold.
What Is DHS Actually Building?
The HART System: Background and Current Status
Definition: The Homeland Advanced Recognition Technology (HART) system is the cloud-based replacement for IDENT (Automated Biometric Identification System), DHS's legacy biometric database. HART is hosted on Amazon Web Services (AWS) and is designed to store and process hundreds of millions of biometric records linked to immigration history, criminal justice data, and travel records.
The GAO (Government Accountability Office) identified significant program management shortcomings in HART in a 2023 audit. In 2025, DHS reorganized biometric oversight under its Chief Information Officer (CIO) to accelerate HART's delivery. Congress subsequently allocated $271.7 million to OBIM to fund expanded capabilities.
The February 2026 RFI takes this further. Rather than simply completing HART, DHS is now asking industry how to build a single enterprise-wide biometric matching engine that would:
- Accept multimodal inputs: face images, fingerprints, palm prints, iris scans, voiceprints, and biographic augmentation data.
- Run real-time and batch matching simultaneously.
- Support both identity verification (one-to-one) and investigative search (one-to-many).
- Serve all DHS components under one enterprise license.
Why Does This Affect Your Business in Alabama?
1. Biometric Data Value Is Rising — And So Is Targeting
Unlike a password or a credit card number, a fingerprint cannot be changed after a breach. Once compromised, it is compromised forever. When the government signals that biometric data is worth this kind of infrastructure investment, the cybercrime economy responds.
The Identity Theft Resource Center's 2025 Business Impact Report found that 81% of small businesses reported a security or data breach in the preceding 12 months. Of those breached, 62.5% faced total financial impacts exceeding $250,000.
2. You May Already Be Holding Biometric Data
Most small business owners, when asked "Does your business handle biometric data?" say no. Then they describe their systems. Here are common business contexts where biometric data is already in play:
| Business Type | Biometric Use Case | Compliance Risk |
|---|---|---|
| Healthcare & Dental | Fingerprint patient check-in; EHR access | HIPAA (biometrics = PHI if linked to patient record) |
| Any business with employees | Windows Hello, Apple Face ID on company devices | State biometric privacy laws (BIPA, CUBI, BPPA) |
| Government contractors | Biometric records collected during federal work | CMMC / NIST 800-171 (Qualifies as CUI) |
| Law/Financial firms | Authentication for secure document vaults | ABA ethics rules; FINRA; GLBA |
| HR/Payroll systems | Fingerprint time clocks | Illinois BIPA; Texas CUBI |
3. The Scope Creep Problem — and What It Means for Your Vendors
The average small business uses 50 to 200 cloud-based SaaS applications. If any one of those vendors collects biometric data from your employees or customers and suffers a breach, your business may bear legal liability. According to IBM's 2025 Cost of a Data Breach Report, vendor and supply chain breaches cost organizations an average of $4.91 million.
What Biometric Privacy Laws Already Apply to Your Business
- Illinois BIPA (Biometric Information Privacy Act): The strictest privacy law in the U.S. Applies to any private entity doing business in Illinois or with Illinois employees — including companies headquartered elsewhere. Penalties run $1,000–$5,000 per individual scan.
- Texas CUBI & Washington BPPA: Both require notice and affirmative consent before collecting biometric data.
What we still need: As of this writing, Alabama has not enacted a standalone biometric privacy law. However, Alabama businesses with employees, vendors, or customers in Illinois, Texas, or Washington are already subject to those states' laws.
Common Mistakes Alabama Businesses Make With Biometric Data
- Assuming "We're Too Small to Be a Target": 43% of all cyberattacks specifically target small businesses.
- Using Biometric Authentication Without a Storage Inventory: Deploying fingerprint readers without documenting where templates are stored violates multiple state privacy laws.
- Treating Vendor Agreements as IT's Problem: Vendor risk management is a legal and business function.
- Waiting for a Breach to Get a Risk Assessment: A proactive assessment costs a fraction of the $250,000+ cost of a breach response.
Step-by-Step: What to Do Right Now
- Inventory your biometric touchpoints: Ask your IT team if any system collects fingerprints, facial images, or voice data.
- Check your vendor contracts: Review SaaS agreements for biometric clauses.
- Identify compliance frameworks: Check your exposure to HIPAA, BIPA, CMMC, etc.
- Schedule a Cybersecurity Risk Assessment: Get a baseline of your vulnerabilities.
- Implement foundational controls: Prioritize MFA, dark web monitoring, and next-generation EDR immediately.
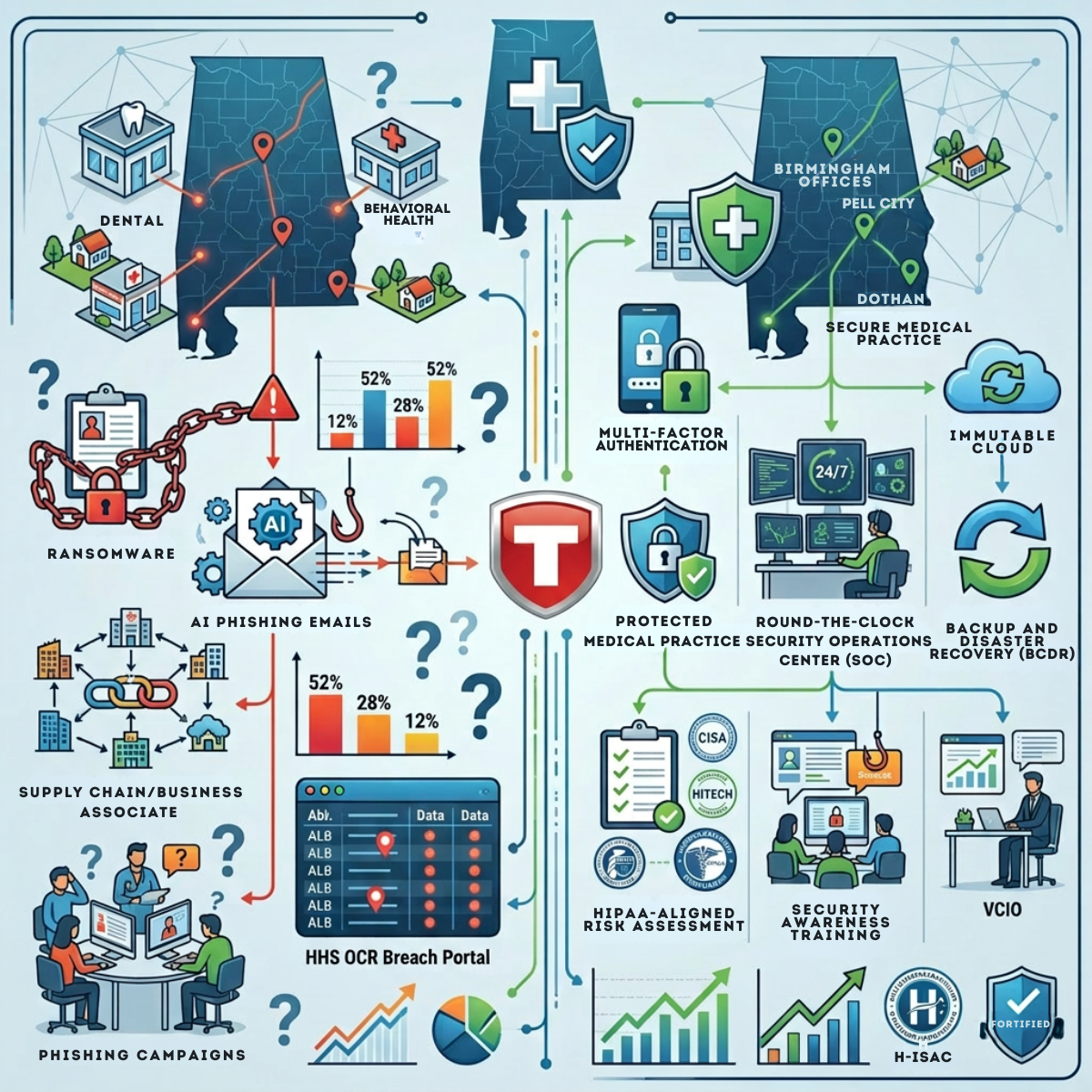
AllTech IT Solutions vs. Typical IT Providers
Who Should Choose AllTech IT Solutions?
- Alabama and Southeast SMBs that handle regulated data (biometric, health, financial, federal contract).
- Healthcare and dental practices needing HIPAA compliance.
- Government contractors requiring CMMC certification.
- Law/financial firms with strict client data obligations.
- Businesses needing an executive-level IT strategy (vCIO).
Who Might Choose a Different Provider?
- Businesses with an existing enterprise IT department needing only narrow, specific supplemental services.
- Organizations outside the Southeast that need a locally based provider in another region.
- Businesses with highly specialized defense/manufacturing OT environments.
Note: AllTech's co-managed IT model can still supplement internal teams effectively.
Ready to get your answers?
Schedule a free Cybersecurity Risk Assessment with AllTech IT Solutions. No obligation. Real data. Clear next steps.
📞 Birmingham (HQ):(205) 290-0215 | Dothan:(334) 794-8705 | Pell City:(205) 338-2946
📧 sales@alltechsupport.com | 🌐 alltechsupport.com
AllTech IT Solutions — Protecting Alabama businesses since 2004. Ranked #1 in Computer Security in Alabama, Best of BusinessRate 2025.
Frequently Asked Questions
- What is DHS's unified biometric search engine?
- The Department of Homeland Security issued RFI No. 70RDA126RFI000003 on February 13, 2026, seeking industry proposals for a single enterprise-wide biometric matching platform across CBP, ICE, TSA, USCIS, and the Secret Service.
- How does the DHS biometric database affect small businesses?
- When government agencies treat biometric data as high-value national infrastructure, that data becomes a premium target for cybercriminals. Any business storing fingerprints, facial recognition data, or iris scans holds data that is increasingly targeted.
- What is Illinois BIPA, and does it affect Alabama businesses?
- Illinois BIPA requires written consent before collecting biometric data. It applies to any entity doing business in Illinois or with Illinois employees — including companies headquartered in other states. Penalties run up to $5,000 per scan.
- What is CMMC and why does it matter for Alabama government contractors?
- CMMC is the DoD's framework for protecting Controlled Unclassified Information (CUI). Any business contracting directly with the DoD or serving as a subcontractor must implement NIST 800-171 controls and achieve CMMC certification.
- Is biometric data different from other personal data for cybersecurity purposes?
- Yes, in one critical way: biometric data is permanent. A stolen password can be reset. A stolen fingerprint or facial geometry template cannot be revoked or replaced. This permanence makes biometric data catastrophically damaging when breached.