Healthcare Is Under Siege in 2026: What Alabama Businesses Need to Know—and Do—Right Now
If you’re running or managing any kind of healthcare operation in Alabama—a medical practice, dental office, behavioral health clinic, specialty provider, or anything that touches patient data—the news in 2026 is not great. Not in a “read our scary blog post” kind of way. In a very real, “this can damage or end your business” way.
The HHS Office for Civil Rights (OCR) breach portal is already logging 2026 incidents, and multiple Alabama-based covered entities have shown up in that database as of this writing. Nationally, ransomware remains the dominant attack vector—accounting for roughly 52% of healthcare cybersecurity incidents so far this year—while enforcement pressure continues to rise.
So we hear one question more than any other from Alabama healthcare owners: “Is this really something I need to worry about?”
Yes. Full stop. Here’s why—and what you can do about it.
The 2026 Threat Landscape: What the Data Actually Says
Let’s start with the numbers, because they tell the story better than any alarm bell.
The HHS OCR Breach Portal is the legally mandated public record for HIPAA-covered breaches affecting 500 or more people. It’s searchable by state, organization name, incident type, and whether a business associate was involved. In other words: it’s a public, searchable record of which healthcare organizations have been compromised.
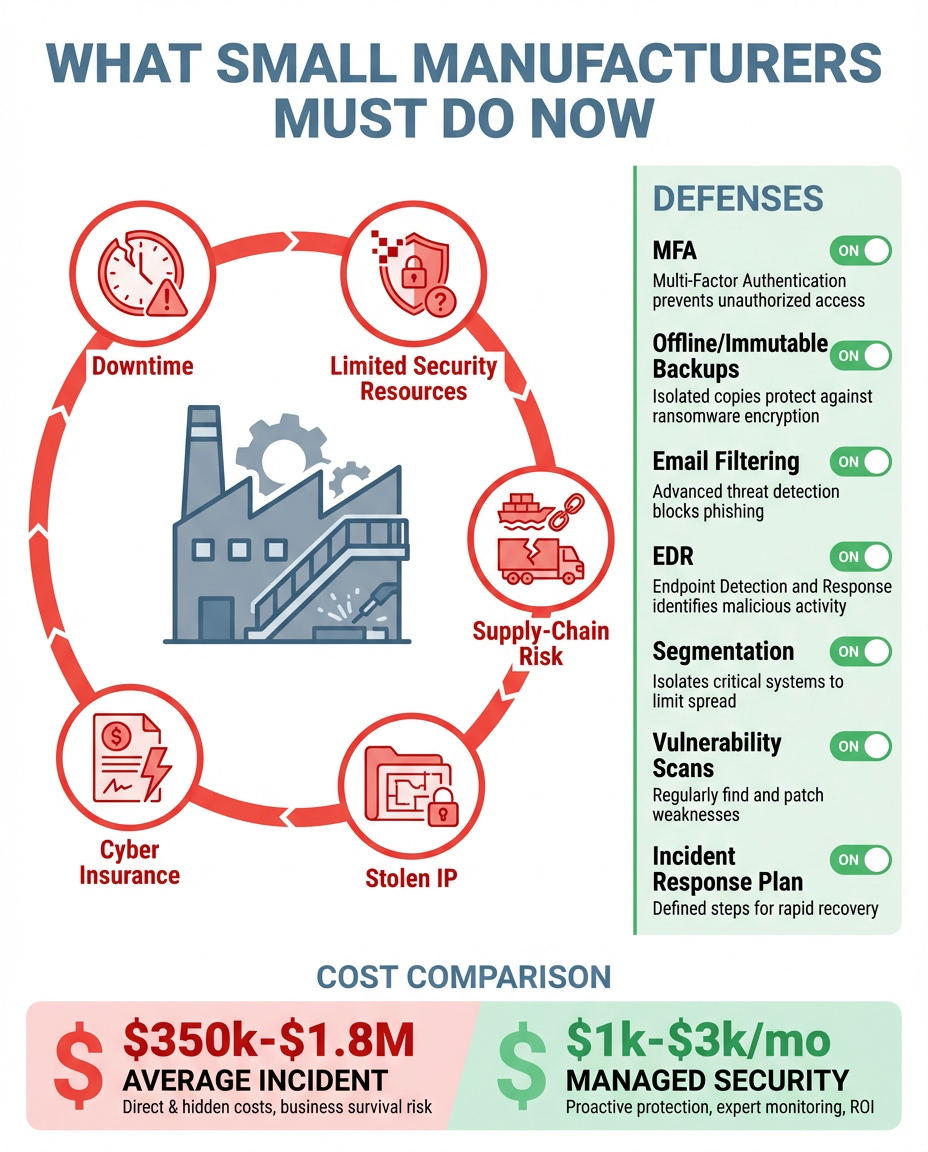
HHS’s Health Sector Cybersecurity Coordination Center (HC3) has identified four active threat categories dominating 2026:
- Ransomware-as-a-Service (RaaS) groups specifically targeting hospitals and healthcare networks
- Phishing campaigns designed to harvest healthcare employee credentials
- Third-party and vendor supply chain attacks that breach you through a trusted partner
- AI-assisted social engineering using artificial intelligence to craft highly convincing emails, voicemails, and text messages
Key takeaway
AI-assisted phishing has changed the game. Messages can convincingly impersonate your billing company, your EHR vendor, your insurer, or even your own staff—so “spot the weird email” is no longer a reliable defense on its own.
Nationally, Q1 2026 attack vectors break down roughly as follows: ransomware and hacking around 52%; phishing and email compromise about 28%; insider threats and human error around 12%; and physical device theft and other causes making up the remaining 8%.
One number that tends to make leadership teams go quiet: the average healthcare data breach—when you add up penalties, regulatory response, legal fees, notification costs, and business disruption—runs about $10.9 million. For many small practices, that’s not just a financial hit. It’s a business-ending event.
Alabama Is Not Exempt, and Your Business Associates Are a Vulnerability Too
A common misconception in Alabama’s small and mid-sized healthcare market is that cybercriminals only target large hospital systems. That’s not true anymore.
Physician groups, outpatient clinics, and specialty providers—including behavioral health, dental, and vision practices—are frequently targeted precisely because they’re perceived as less defended: fewer IT resources, older software, and no dedicated security staff.
And there’s a vulnerability that catches many organizations off guard: your business associates.
HIPAA defines a Business Associate as any vendor or third party that creates, receives, maintains, or transmits protected health information (PHI) on your behalf—billing, transcription, cloud storage, IT vendors, answering services, and more. If a business associate is breached and your patients’ data is exposed, you still bear regulatory responsibility.
Supply chain incidents can create outsized exposure: one compromised vendor can trigger breach notifications for dozens of covered entities at once. If you don’t have current, enforceable Business Associate Agreements (BAAs) in place for every vendor that touches PHI, you likely have a compliance gap—and you may not find out until an investigator calls.
The Regulatory Environment Is Getting Harder, Not Easier
OCR isn’t just tracking breaches. It’s enforcing more aggressively.
The HIPAA Security Rule modernization proposals introduced in 2024 and 2025 are being implemented now, with heightened scrutiny on MFA enforcement, encryption of PHI at rest, and the adequacy of BAAs. HIPAA violations can run up to $1.9 million per incident category.
At the same time, CISA has published Healthcare Cybersecurity Performance Goals—voluntary benchmarks that are increasingly referenced during investigations as an expected standard of care. Practically, that means “we didn’t know” isn’t a defensible posture anymore.
Being breached is bad. Being breached without demonstrable security controls and documentation is catastrophic. The difference between a manageable investigation and a seven-figure penalty often comes down to whether you can document that you took reasonable, proactive steps to protect PHI.
“Okay, But What Do We Actually Do About This?”
That’s the question AllTech was built to answer.
AllTech has served Alabama businesses since 2004. We’re an Alabama company with offices in Birmingham, Dothan, and Pell City, serving healthcare organizations like yours.
Here’s what protecting a healthcare organization in 2026 looks like in practice:
- Multi-Factor Authentication (MFA)—now.
MFA blocks the vast majority of credential-based attacks. OCR is scrutinizing MFA in breach investigations, and for good reason. If you don’t have it everywhere you need it, that’s where we start.
- 24/7 Security Operations Center (SOC) monitoring.
Ransomware and phishing don’t respect business hours. Continuous monitoring, endpoint detection/response, and email security reduce dwell time and limit blast radius.
- Backups and disaster recovery that are actually tested.
Ransomware becomes a catastrophe when backups are incomplete, untested, or encrypted too. Immutable, geo-redundant backups and regular restoration testing matter—along with documented RTO/RPO.
- A HIPAA-aligned risk assessment.
You can’t fix what you can’t see. A formal assessment provides a gap analysis mapped to HIPAA/HITECH requirements and a prioritized remediation plan.
- Security awareness training that works.
Healthcare-targeted phishing remains a top threat. Ongoing training plus phishing simulations reduce human-driven risk and produce documentation for audits and insurance.
- A vCIO who understands healthcare compliance.
Most small and mid-sized practices can’t justify a full-time CIO. vCIO services provide strategy, compliance oversight, vendor management, and board-ready reporting.
The Question You Should Really Be Asking Right Now
It’s not “could this happen to me?” It’s already happening—across Alabama and across the Southeast.
The real question is: if ransomware encrypted your systems tonight, what would happen tomorrow morning?
If your answer involves uncertainty, improvisation, or a frantic call to a vendor who doesn’t really know your environment, that’s the gap we’re here to close.
What to Do Next
AllTech recommends one low-friction first step: a Cybersecurity Risk Assessment tailored to your healthcare environment. We’ll identify vulnerabilities, map your posture against HIPAA requirements, and deliver a clear prioritized report—no obligation to proceed further.
- Birmingham (HQ):(205) 290-0215 | 500 Chase Park South, Suite 200, Hoover, AL 35244
- Dothan:(334) 794-8705 | 331 Ross Clark Circle, Dothan, AL 36303
- Pell City:(205) 338-2946 | 207 Cogswell Ave, Pell City, AL 35125
- Email: sales@alltechsupport.com
- Web: alltechsupport.com
Next step
Need help protecting patient data in 2026?
If you’re not sure where your biggest HIPAA and cybersecurity gaps are, a risk assessment is the fastest way to get clarity and a prioritized plan.
References
- AllTech IT Solutions. AI Sales Agent - Comprehensive Knowledge Base. Version 1.0, Feb. 2026.
- American Hospital Association. “Cybersecurity Resources and Guidance.” https://www.aha.org/cybersecurity
- Cybersecurity and Infrastructure Security Agency. “Healthcare Cybersecurity Performance Goals.” https://www.cisa.gov/healthcare
- Fortified Health Security. “2026 Annual Report on Healthcare Cybersecurity.” https://www.fortifiedhealthsecurity.com
- Health Information Sharing and Analysis Center. “2026 Threat Intelligence Advisories.” https://www.h-isac.org
- HIPAA Journal. “Healthcare Data Breach Barometer - Q1 2026.” https://www.hipaajournal.com
- HHS Health Sector Cybersecurity Coordination Center (HC3). “2026 Threat Briefings and Sector Alerts.” https://www.hhs.gov/about/agencies/asa/ocio/hc3/index.html
- HHS Office for Civil Rights. “HHS OCR Breach Portal - 2026 Breach Report Database.” https://ocrportal.hhs.gov/ocr/breach/breach_report.jsf
AllTech IT Solutions has been protecting Alabama businesses since 2004. Ranked #1 for Computer Security in Alabama (Best of BusinessRate 2025) and #2,582 on the Inc. 5000. 99.3/100 CSAT. Three Alabama offices. One mission: End the IT Chaos.